Introduction
Data Encryption Tools help organizations protect sensitive data by converting it into unreadable formats that can only be accessed with the correct decryption key. These tools are essential for securing data at rest, in transit, and in use across systems, applications, and cloud environments.
With increasing cyber threats, ransomware attacks, and strict data privacy regulations, encryption has become a core security requirement for modern businesses. Today’s encryption tools use advanced algorithms, key management systems, and automation to ensure data confidentiality, integrity, and compliance.
Common use cases include:
- Encrypting sensitive files and databases
- Securing cloud storage and communications
- Protecting customer and financial data
- Ensuring regulatory compliance (GDPR, HIPAA, etc.)
- Secure file sharing and backup protection
Key evaluation criteria:
- Encryption standards (AES, RSA, etc.)
- Key management capabilities
- Ease of integration
- Performance and speed impact
- Cloud and on-prem support
- Compliance certifications
- Scalability
- Usability and automation
Best for: Enterprises, financial institutions, healthcare organizations, and any business handling sensitive or regulated data.
Not ideal for: Basic personal use cases that do not involve sensitive or regulated data.
Key Trends in Data Encryption Tools
- Widespread adoption of zero-trust security models
- Integration with cloud-native environments
- Automated key management systems (KMS)
- End-to-end encryption for applications and APIs
- Quantum-resistant encryption development
- Data-in-use encryption technologies emerging
- Increased regulatory pressure for encryption standards
- Hardware-based encryption acceleration
- Seamless DevSecOps integration
- Focus on user-friendly encryption automation
How We Evaluated Data Encryption Tools (Methodology)
- Assessed encryption strength and algorithms used
- Evaluated key management capabilities
- Reviewed integration with enterprise systems
- Considered performance impact and scalability
- Assessed security certifications and compliance support
- Evaluated ease of use and deployment flexibility
- Considered platform compatibility (cloud, on-prem, hybrid)
- Assessed enterprise adoption and reliability
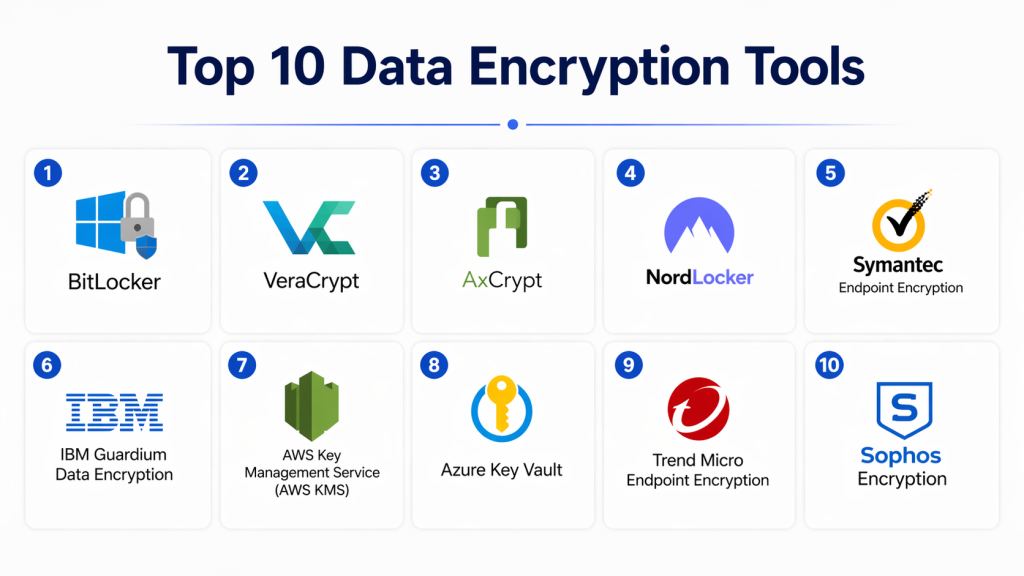
Top 10 Data Encryption Tools
#1 — BitLocker
Short description: A built-in Windows encryption tool used for full disk encryption. Widely adopted in enterprise environments. Provides strong protection for data at rest. Easy to deploy within Windows ecosystems. Ideal for endpoint security.
Key Features
- Full disk encryption
- TPM integration
- Secure boot support
- Recovery key management
- Policy-based enforcement
Pros
- Built into Windows
- Easy to use
Cons
- Limited to Windows
- Basic advanced features
Platforms / Deployment
Windows
Security & Compliance
AES encryption, TPM support (others not publicly stated)
Integrations & Ecosystem
- Microsoft ecosystem
- Enterprise IT tools
Support & Community
Strong Microsoft support.
#2 — VeraCrypt
Short description: An open-source encryption tool used for disk and volume encryption. Known for strong security and flexibility. Popular among security professionals.
Key Features
- Disk encryption
- Volume encryption
- Hidden volumes
- Cross-platform support
- Strong algorithms
Pros
- Free and open-source
- Strong security
Cons
- Complex interface
- No enterprise support
Platforms / Deployment
Windows / macOS / Linux
Security & Compliance
AES, Serpent, Twofish encryption
Integrations & Ecosystem
- File systems
- External storage
Support & Community
Community-based support.
#3 — AxCrypt
Short description: A simple file encryption tool designed for individual users and small teams. Focuses on ease of use and secure file sharing.
Key Features
- File encryption
- Password protection
- Cloud integration
- Key management
- Secure sharing
Pros
- Easy to use
- Lightweight
Cons
- Limited enterprise features
- Requires subscription for full features
Platforms / Deployment
Windows / macOS / Mobile
Security & Compliance
AES-256 encryption
Integrations & Ecosystem
- Cloud storage platforms
- File systems
Support & Community
Good support.
#4 — NordLocker
Short description: A modern encryption tool offering secure file storage and sharing. Designed for personal and business use. Focuses on cloud-based encryption.
Key Features
- File encryption
- Cloud storage encryption
- Secure sharing
- Zero-knowledge architecture
- Backup encryption
Pros
- User-friendly
- Strong privacy focus
Cons
- Subscription-based
- Limited enterprise controls
Platforms / Deployment
Windows / macOS / Cloud
Security & Compliance
End-to-end encryption
Integrations & Ecosystem
- Cloud storage
- Devices
Support & Community
Good support.
#5 — Symantec Encryption (PGP)
Short description: Enterprise-grade encryption solution widely used for email and data protection. Known for strong cryptographic standards and enterprise adoption.
Key Features
- Email encryption
- File encryption
- Key management
- Disk encryption
- Policy enforcement
Pros
- Enterprise-grade security
- Strong reputation
Cons
- Complex deployment
- High cost
Platforms / Deployment
Windows / Enterprise systems
Security & Compliance
PGP encryption standards
Integrations & Ecosystem
- Enterprise email systems
- APIs
Support & Community
Enterprise support.
#6 — IBM Guardium Data Encryption
Short description: A robust enterprise encryption platform focusing on database and application-level security. Suitable for large organizations.
Key Features
- Database encryption
- Key management
- Policy control
- Monitoring
- Compliance reporting
Pros
- Strong enterprise focus
- Scalable
Cons
- Complex setup
- Expensive
Platforms / Deployment
Cloud / On-prem
Security & Compliance
AES encryption, enterprise compliance support
Integrations & Ecosystem
- Databases
- Enterprise apps
Support & Community
Enterprise support.
#7 — Microsoft Azure Key Vault
Short description: A cloud-based key management and encryption service used for securing applications and data in Azure environments.
Key Features
- Key management
- Secret storage
- Encryption services
- Access control
- Monitoring
Pros
- Strong Azure integration
- Scalable
Cons
- Azure dependency
- Requires cloud expertise
Platforms / Deployment
Cloud
Security & Compliance
FIPS-compliant encryption
Integrations & Ecosystem
- Azure services
- DevOps tools
Support & Community
Microsoft support.
#8 — AWS Key Management Service (KMS)
Short description: A managed encryption key service for AWS cloud environments. Provides secure key creation and control for cloud applications.
Key Features
- Key generation
- Key management
- Encryption APIs
- Access control
- Audit logs
Pros
- Deep AWS integration
- Highly scalable
Cons
- AWS ecosystem lock-in
- Requires expertise
Platforms / Deployment
Cloud
Security & Compliance
AES encryption standards
Integrations & Ecosystem
- AWS services
- APIs
Support & Community
Strong AWS support.
#9 — Boxcryptor (now Dropbox Encryption)
Short description: A file encryption tool designed for cloud storage security. Focuses on securing files before uploading to cloud services.
Key Features
- File encryption
- Cloud integration
- Secure sharing
- Access control
- Multi-platform support
Pros
- Easy cloud integration
- Strong usability
Cons
- Limited enterprise features
- Subscription required
Platforms / Deployment
Cloud / Desktop
Security & Compliance
End-to-end encryption
Integrations & Ecosystem
- Cloud storage platforms
- APIs
Support & Community
Good support.
#10 — Trend Micro Endpoint Encryption
Short description: A security-focused encryption solution for endpoints and enterprise devices. Offers strong data protection and centralized management.
Key Features
- Endpoint encryption
- Full disk encryption
- Centralized management
- Policy enforcement
- Reporting
Pros
- Strong enterprise security
- Centralized control
Cons
- Complex setup
- Premium pricing
Platforms / Deployment
Windows / Enterprise
Security & Compliance
AES encryption, compliance support
Integrations & Ecosystem
- Endpoint security tools
- Enterprise systems
Support & Community
Enterprise support.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| BitLocker | Windows users | Windows | On-prem | Built-in encryption | N/A |
| VeraCrypt | Advanced users | Win/Mac/Linux | On-prem | Open-source security | N/A |
| AxCrypt | SMB | Desktop | Cloud/Desktop | Simplicity | N/A |
| NordLocker | Personal/SMB | Web/Desktop | Cloud | Secure cloud storage | N/A |
| Symantec PGP | Enterprise | Windows | On-prem | Email encryption | N/A |
| IBM Guardium | Enterprise | Web | Hybrid | Database security | N/A |
| Azure Key Vault | Cloud users | Web | Cloud | Key management | N/A |
| AWS KMS | AWS users | Web | Cloud | AWS integration | N/A |
| Boxcryptor | Cloud storage | Web/Desktop | Cloud | File protection | N/A |
| Trend Micro | Enterprise | Desktop | Hybrid | Endpoint encryption | N/A |
Evaluation & Scoring of Data Encryption Tools
| Tool | Core | Ease | Integrations | Security | Performance | Support | Value | Total |
|---|---|---|---|---|---|---|---|---|
| BitLocker | 8 | 9 | 8 | 8 | 9 | 8 | 9 | 8.4 |
| VeraCrypt | 9 | 6 | 7 | 9 | 8 | 7 | 10 | 8.0 |
| AxCrypt | 7 | 9 | 7 | 8 | 8 | 7 | 9 | 7.9 |
| NordLocker | 8 | 9 | 8 | 9 | 8 | 8 | 8 | 8.3 |
| Symantec PGP | 9 | 6 | 8 | 9 | 8 | 8 | 7 | 8.0 |
| IBM Guardium | 9 | 6 | 9 | 9 | 8 | 8 | 7 | 8.3 |
| Azure Key Vault | 9 | 8 | 9 | 9 | 9 | 9 | 8 | 8.7 |
| AWS KMS | 9 | 8 | 9 | 9 | 9 | 9 | 8 | 8.7 |
| Boxcryptor | 8 | 9 | 8 | 8 | 8 | 7 | 8 | 8.1 |
| Trend Micro | 8 | 7 | 8 | 9 | 8 | 8 | 7 | 8.0 |
Which Data Encryption Tool Is Right for You?
Solo / Freelancer
AxCrypt or VeraCrypt are simple and affordable.
SMB
NordLocker or AxCrypt are easy and practical.
Mid-Market
Boxcryptor or Trend Micro offer balanced features.
Enterprise
IBM Guardium, AWS KMS, and Azure Key Vault are top choices.
Budget vs Premium
- Budget: VeraCrypt
- Premium: IBM Guardium
Feature Depth vs Ease of Use
- Easy: BitLocker
- Advanced: AWS KMS
Integrations & Scalability
- Best integrations: AWS KMS, Azure Key Vault
Security & Compliance
- High compliance: IBM Guardium, Symantec PGP
FAQs
1. What are data encryption tools?
Data encryption tools convert readable data into unreadable formats to protect it from unauthorized access. Only authorized users can decrypt and access the data. These tools are essential for data security and privacy. They are widely used in enterprises and cloud environments.
2. Why is encryption important?
Encryption protects sensitive data from cyberattacks and breaches. It ensures confidentiality and data integrity. It is also required for regulatory compliance. Without encryption, data is vulnerable.
3. Are encryption tools expensive?
Pricing varies based on features and usage. Some tools are free, while enterprise solutions are expensive. Organizations choose based on security needs.
4. Can encryption slow down systems?
Yes, encryption can slightly impact performance. However, modern tools are optimized. The impact is usually minimal.
5. Do encryption tools support cloud systems?
Yes, most modern tools support cloud environments. Cloud encryption is widely used today. Integration varies by provider.
6. What is key management?
Key management involves creating, storing, and controlling encryption keys. It is critical for secure encryption systems. Poor key management weakens security.
7. Are encryption tools secure?
Yes, they use strong algorithms like AES and RSA. Security depends on proper configuration. Trusted tools are highly secure.
8. Can encryption be broken?
Modern encryption is extremely difficult to break. It would take enormous computing power. Proper implementation ensures safety.
9. What are common challenges?
Challenges include key management and integration complexity. Proper setup reduces risks. Training is important.
10. What are alternatives to encryption tools?
Alternatives include basic password protection, but they are weak. Encryption is the most secure method. It is industry standard.
Conclusion
Data encryption tools are a fundamental part of modern cybersecurity strategies, ensuring that sensitive information remains protected across devices, networks, and cloud environments. As cyber threats continue to evolve and data privacy regulations become stricter, encryption has become a non-negotiable requirement for organizations of all sizes. These tools provide the essential layer of defense needed to secure data at rest, in transit, and in use.
Choosing the right encryption solution depends on your environment, security needs, and technical expertise. Enterprises often rely on advanced platforms like AWS KMS, Azure Key Vault, or IBM Guardium, while individuals and SMBs can use simpler tools like VeraCrypt or AxCrypt. The key is to balance usability, security strength, and integration capabilities to build a strong and scalable data protection strategy.