Introduction
Key Management Systems (KMS) are critical security platforms that help organizations create, store, manage, rotate, and control encryption keys used to protect sensitive data. These systems ensure that cryptographic keys are securely handled across cloud, on-premises, and hybrid environments.
As organizations increasingly adopt cloud computing, encryption, and zero-trust security models, managing encryption keys has become a core requirement. Without proper key management, even strong encryption can be compromised. Modern KMS solutions provide centralized control, automation, compliance support, and integration with cloud services and applications.
Common use cases include:
- Encrypting cloud and on-prem data
- Managing SSL/TLS certificates and keys
- Securing databases and applications
- Supporting compliance (GDPR, HIPAA, PCI-DSS)
- Enabling zero-trust security architectures
Key evaluation criteria:
- Key lifecycle management capabilities
- Encryption standards and algorithms
- Cloud and hybrid support
- Integration with applications and services
- Automation and rotation policies
- Security and access control mechanisms
- Compliance certifications
- Scalability and performance
Best for: Enterprises, cloud-native companies, financial institutions, and organizations handling sensitive or regulated data.
Not ideal for: Small businesses with minimal encryption requirements or no cloud infrastructure.
Key Trends in Key Management Systems (KMS)
- Cloud-native and multi-cloud key management adoption
- Automation of key rotation and lifecycle management
- Integration with zero-trust security frameworks
- Hardware Security Modules (HSM) integration
- Support for hybrid and multi-cloud environments
- API-first key management architectures
- Quantum-resistant encryption research and adoption
- Centralized governance for cryptographic assets
- Improved DevSecOps integration
- Compliance-driven key auditing and reporting
How We Evaluated Key Management Systems (KMS) (Methodology)
- Assessed key lifecycle management capabilities
- Evaluated security strength and encryption standards
- Reviewed integration with cloud and enterprise systems
- Considered automation and scalability features
- Assessed compliance and regulatory support
- Evaluated ease of deployment and usability
- Considered performance and latency impact
- Assessed enterprise adoption and reliability
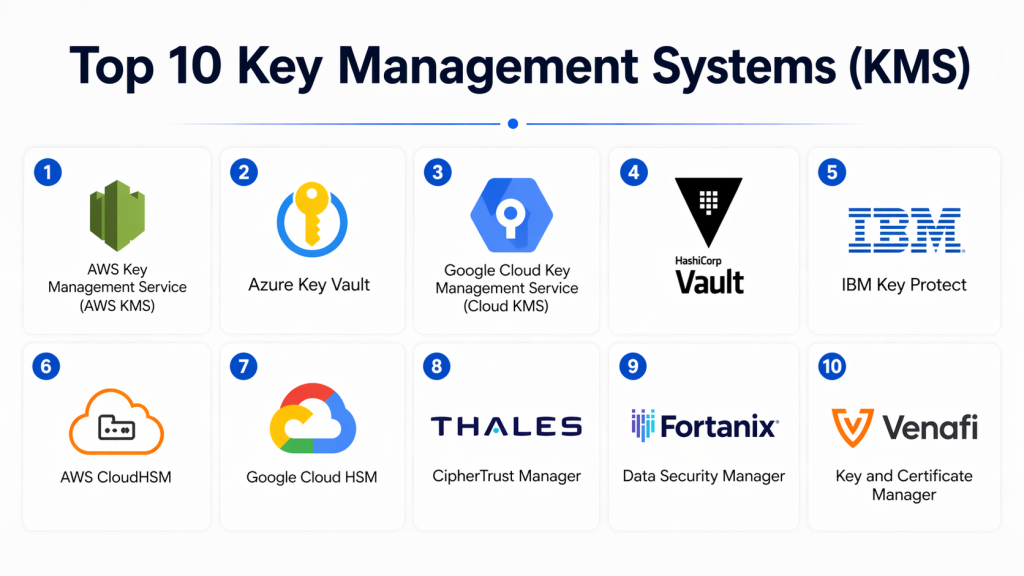
Top 10 Key Management Systems (KMS)
#1 — AWS Key Management Service (AWS KMS)
Short description: A fully managed cloud-based key management service from AWS. It enables secure creation and control of encryption keys across AWS services. Highly scalable and widely adopted in cloud-native environments. Supports automated key rotation and fine-grained access control. Ideal for AWS users.
Key Features
- Key creation and management
- Automatic key rotation
- Access control policies
- Encryption APIs
- Audit logging
Pros
- Deep AWS integration
- Highly scalable
Cons
- AWS ecosystem dependency
- Requires cloud expertise
Platforms / Deployment
Cloud
Security & Compliance
FIPS 140-2 validated encryption (others not publicly stated)
Integrations & Ecosystem
- AWS services
- DevOps tools
- APIs
Support & Community
Strong AWS enterprise support.
#2 — Azure Key Vault
Short description: A cloud-based KMS from Microsoft Azure that securely stores and manages cryptographic keys, secrets, and certificates. Designed for enterprise-grade cloud security. Offers strong integration with Azure ecosystem.
Key Features
- Key and secret storage
- Certificate management
- Access control (RBAC)
- Logging and monitoring
- API-based access
Pros
- Strong Azure integration
- Enterprise-ready
Cons
- Azure ecosystem dependency
- Requires cloud knowledge
Platforms / Deployment
Cloud
Security & Compliance
FIPS-compliant encryption (others not publicly stated)
Integrations & Ecosystem
- Azure services
- Enterprise applications
- APIs
Support & Community
Microsoft enterprise support.
#3 — Google Cloud KMS
Short description: A managed key management service from Google Cloud offering secure encryption key handling. Designed for multi-cloud and hybrid environments. Supports integration with Google services.
Key Features
- Key lifecycle management
- Encryption/decryption APIs
- IAM-based access control
- Audit logging
- Automated rotation
Pros
- Strong Google Cloud integration
- Easy API access
Cons
- GCP ecosystem dependency
- Limited offline use
Platforms / Deployment
Cloud
Security & Compliance
Industry-standard encryption support
Integrations & Ecosystem
- Google Cloud services
- APIs
Support & Community
Google Cloud support.
#4 — HashiCorp Vault
Short description: A widely used open-source and enterprise-grade secrets and key management platform. Supports dynamic secrets, encryption, and policy-based access control. Popular in DevOps and cloud-native environments.
Key Features
- Secrets management
- Key lifecycle control
- Dynamic secrets
- Policy-based access
- Encryption as a service
Pros
- Highly flexible
- Strong DevSecOps integration
Cons
- Complex setup
- Requires expertise
Platforms / Deployment
Cloud / On-prem / Hybrid
Security & Compliance
Encryption, audit logging
Integrations & Ecosystem
- Kubernetes
- CI/CD pipelines
- Cloud platforms
Support & Community
Strong open-source and enterprise support.
#5 — IBM Key Protect
Short description: A cloud-based key management service from IBM Cloud designed for enterprise-grade encryption key control. Offers integration with IBM ecosystem and hybrid cloud environments.
Key Features
- Key lifecycle management
- Encryption services
- Access control
- Audit logging
- API integration
Pros
- Strong enterprise security
- Hybrid cloud support
Cons
- IBM ecosystem dependency
- Complex configuration
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
Enterprise-grade encryption standards
Integrations & Ecosystem
- IBM Cloud services
- APIs
Support & Community
IBM enterprise support.
#6 — AWS CloudHSM
Short description: A hardware-based key management system from AWS providing dedicated Hardware Security Modules (HSMs). Designed for high-security workloads requiring physical key isolation.
Key Features
- Dedicated HSMs
- Key generation and storage
- Strong encryption
- API access
- Compliance support
Pros
- High security level
- Hardware-based protection
Cons
- Expensive
- Complex setup
Platforms / Deployment
Cloud
Security & Compliance
FIPS 140-2 Level 3 compliance
Integrations & Ecosystem
- AWS services
- Enterprise applications
Support & Community
AWS enterprise support.
#7 — Google Cloud HSM
Short description: A hardware security module service from Google Cloud providing secure cryptographic key storage. Designed for high-security and compliance-heavy workloads.
Key Features
- Hardware-based key storage
- Encryption operations
- Access control
- Audit logging
- API integration
Pros
- Strong security
- Google Cloud integration
Cons
- Higher cost
- Cloud dependency
Platforms / Deployment
Cloud
Security & Compliance
FIPS 140-2 Level 3 compliance
Integrations & Ecosystem
- Google Cloud services
- APIs
Support & Community
Google Cloud support.
#8 — Thales CipherTrust Manager
Short description: An enterprise key management platform offering centralized encryption key control. Widely used in regulated industries for data protection and compliance.
Key Features
- Key lifecycle management
- Encryption control
- Centralized policy management
- Audit logging
- Multi-cloud support
Pros
- Strong enterprise security
- Multi-cloud support
Cons
- Complex deployment
- Premium pricing
Platforms / Deployment
Cloud / On-prem / Hybrid
Security & Compliance
Compliance-ready encryption
Integrations & Ecosystem
- Enterprise systems
- Cloud platforms
Support & Community
Enterprise support.
#9 — Fortanix Data Security Manager
Short description: A modern cloud-native KMS offering unified key and secret management. Designed for multi-cloud environments and strong compliance needs.
Key Features
- Key management
- Secrets management
- Encryption APIs
- Access control
- Audit logs
Pros
- Cloud-native design
- Strong scalability
Cons
- Pricing varies
- Learning curve
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
Enterprise encryption standards
Integrations & Ecosystem
- Cloud platforms
- APIs
Support & Community
Good enterprise support.
#10 — Venafi Key and Certificate Manager
Short description: A specialized key and certificate management platform focused on machine identities. Helps manage TLS/SSL certificates and cryptographic keys at scale.
Key Features
- Certificate lifecycle management
- Key management
- Automation
- Policy enforcement
- Monitoring
Pros
- Strong certificate management
- Enterprise automation
Cons
- Narrow focus
- Complex for small teams
Platforms / Deployment
Cloud / On-prem
Security & Compliance
Enterprise-grade encryption support
Integrations & Ecosystem
- DevOps tools
- Enterprise systems
Support & Community
Strong enterprise support.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| AWS KMS | AWS users | Web | Cloud | AWS integration | N/A |
| Azure Key Vault | Microsoft users | Web | Cloud | Secret management | N/A |
| Google Cloud KMS | GCP users | Web | Cloud | IAM control | N/A |
| HashiCorp Vault | DevOps | Web | Hybrid | Secrets engine | N/A |
| IBM Key Protect | Enterprise | Web | Cloud/Hybrid | IBM integration | N/A |
| AWS CloudHSM | High security | Web | Cloud | Hardware security | N/A |
| Google Cloud HSM | Enterprise | Web | Cloud | Hardware encryption | N/A |
| Thales CipherTrust | Regulated industries | Web | Hybrid | Centralized control | N/A |
| Fortanix | Cloud-native | Web | Cloud | Multi-cloud support | N/A |
| Venafi | Certificate mgmt | Web | Hybrid | TLS automation | N/A |
Evaluation & Scoring of KMS Tools
| Tool | Core | Ease | Integrations | Security | Performance | Support | Value | Total |
|---|---|---|---|---|---|---|---|---|
| AWS KMS | 9 | 8 | 9 | 9 | 9 | 9 | 8 | 8.7 |
| Azure Key Vault | 9 | 8 | 9 | 9 | 9 | 9 | 8 | 8.7 |
| Google KMS | 9 | 8 | 9 | 9 | 9 | 8 | 8 | 8.6 |
| HashiCorp Vault | 9 | 7 | 9 | 9 | 8 | 8 | 8 | 8.4 |
| IBM Key Protect | 8 | 7 | 8 | 9 | 8 | 8 | 7 | 8.0 |
| AWS CloudHSM | 9 | 6 | 8 | 10 | 9 | 9 | 7 | 8.4 |
| Google HSM | 9 | 6 | 8 | 10 | 9 | 8 | 7 | 8.3 |
| Thales CipherTrust | 9 | 6 | 8 | 9 | 8 | 8 | 7 | 8.1 |
| Fortanix | 8 | 8 | 8 | 9 | 8 | 8 | 8 | 8.3 |
| Venafi | 8 | 7 | 8 | 9 | 8 | 8 | 7 | 8.1 |
Which Key Management System Is Right for You?
Solo / Freelancer
Not typically required unless working with encryption-heavy systems.
SMB
Fortanix or HashiCorp Vault (simplified setup options)
Mid-Market
Azure Key Vault or Google Cloud KMS
Enterprise
AWS KMS, IBM Key Protect, Thales CipherTrust
Budget vs Premium
- Budget: HashiCorp Vault
- Premium: AWS CloudHSM
Feature Depth vs Ease of Use
- Easy: Azure Key Vault
- Advanced: HashiCorp Vault
Integrations & Scalability
- Best integrations: AWS KMS, Azure Key Vault
Security & Compliance
- Highest security: AWS CloudHSM, Google Cloud HSM
FAQs
1. What is a Key Management System (KMS)?
A KMS is a security system used to create, store, and manage encryption keys. It ensures secure handling of cryptographic keys across systems. It is essential for data protection. It supports encryption workflows in cloud and on-prem environments.
2. Why is KMS important?
KMS ensures that encryption keys are securely managed. Without it, encrypted data can be compromised. It is critical for compliance and security. It reduces the risk of unauthorized access.
3. Who uses KMS tools?
Enterprises, cloud providers, and developers use KMS tools. They are widely used in fintech, healthcare, and IT industries. Any organization using encryption needs KMS.
4. Are KMS tools expensive?
Pricing varies depending on usage and provider. Cloud-based KMS is usually pay-as-you-go. Hardware-based systems are more expensive.
5. Do KMS tools support cloud environments?
Yes, most modern KMS tools are cloud-native. They integrate with AWS, Azure, and Google Cloud. Hybrid support is also common.
6. What is key rotation?
Key rotation is the process of periodically changing encryption keys. It improves security by limiting exposure. Most KMS tools automate this process.
7. Are KMS tools secure?
Yes, they use strong encryption standards and access controls. Security depends on proper configuration. Enterprise tools follow strict compliance standards.
8. Can KMS integrate with applications?
Yes, KMS tools provide APIs for integration. They work with databases, applications, and cloud services. Integration is a core feature.
9. What are common challenges?
Challenges include configuration complexity and cost. Proper setup is required. Training improves effectiveness.
10. What are alternatives to KMS?
Alternatives include manual key storage or basic encryption tools. However, they are not secure or scalable. KMS is the industry standard.
Conclusion
Key Management Systems (KMS) are a foundational component of modern cybersecurity, enabling organizations to securely manage encryption keys across cloud, hybrid, and on-prem environments. As data protection requirements grow and encryption becomes standard practice, KMS platforms ensure that cryptographic keys are properly controlled, rotated, and secured throughout their lifecycle.
Choosing the right KMS depends on your infrastructure, compliance needs, and scalability requirements. Cloud-native solutions like AWS KMS and Azure Key Vault are ideal for modern cloud workloads, while enterprise-grade systems like Thales CipherTrust and IBM Key Protect offer advanced governance and hybrid capabilities. The best approach is to evaluate integration compatibility, security requirements, and operational complexity before selecting a solution.