Introduction
Cloud Access Security Brokers (CASB) act as a security control point between users and cloud services, helping organizations monitor, enforce policies, and protect sensitive data across SaaS, IaaS, and PaaS environments. In simple terms, CASB tools ensure that employees can safely use apps like Microsoft 365, Google Workspace, and Salesforce without exposing the organization to risk.
In the current cybersecurity landscape, CASB has become critical due to remote work, SaaS sprawl, identity-based attacks, and Zero Trust adoption. Organizations are no longer operating within a fixed perimeter, making cloud-native security essential.
Real-world use cases include:
- Preventing data leaks from SaaS apps
- Enforcing access policies based on identity and device
- Detecting shadow IT usage
- Monitoring risky user behavior (insider threats)
- Securing third-party integrations
Evaluation criteria buyers should consider:
- Data protection & DLP capabilities
- Identity & access control integration
- API vs proxy deployment support
- Threat detection and response
- Compliance and audit readiness
- Integration with existing security stack
- Scalability and performance
- Ease of deployment and management
Best for: IT managers, security teams, CISOs, and enterprises managing multiple cloud apps, especially in finance, healthcare, SaaS, and remote-first companies.
Not ideal for: Very small businesses with minimal SaaS usage or those relying solely on endpoint security without complex cloud workflows.
Key Trends in Cloud Access Security Brokers (CASB)
- AI-powered threat detection is improving anomaly detection and insider risk visibility
- Integration with Zero Trust frameworks is becoming standard
- Convergence into SSE (Security Service Edge) platforms combining CASB, SWG, ZTNA
- API-first security models gaining popularity for SaaS visibility without inline latency
- Identity-centric security replacing network-centric approaches
- Real-time policy enforcement across devices and geographies
- Compliance automation for GDPR, HIPAA, and other standards
- Shadow IT discovery enhanced through machine learning
- Multi-cloud visibility across AWS, Azure, GCP environments
- Flexible pricing models shifting toward usage-based billing
How We Evaluated Cloud Access Security Brokers (CASB) (Methodology)
- Assessed market adoption and enterprise usage trends
- Evaluated feature completeness (DLP, access control, threat protection)
- Considered performance and scalability benchmarks
- Reviewed security posture indicators (encryption, IAM integration)
- Analyzed integration ecosystem (SIEM, IAM, endpoints)
- Evaluated deployment flexibility (API, proxy, hybrid)
- Considered customer fit across SMB, mid-market, enterprise
- Reviewed ease of deployment and operational complexity
- Assessed vendor innovation in AI and automation
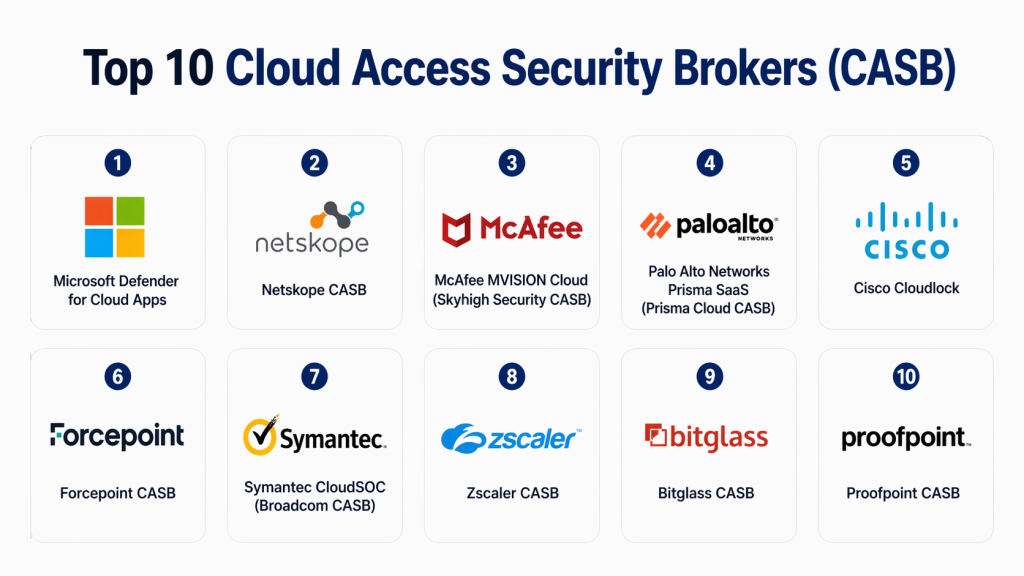
Top 10 Cloud Access Security Brokers (CASB)
#1 — Microsoft Defender for Cloud Apps
Short description: A leading CASB solution integrated within Microsoft’s security ecosystem, designed for organizations using Microsoft 365 and Azure. It offers deep visibility, threat detection, and policy enforcement across cloud apps. Best suited for enterprises already invested in Microsoft environments. Its native integration reduces complexity while enhancing identity-based security. Strong focus on Zero Trust architecture. Ideal for large-scale deployments.
Key Features
- Shadow IT discovery
- Data loss prevention (DLP)
- Conditional access integration
- Threat detection analytics
- API and proxy deployment
- App governance controls
Pros
- Deep Microsoft ecosystem integration
- Strong identity-based controls
Cons
- Limited flexibility outside Microsoft stack
- Complex configuration for beginners
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
SSO, MFA, encryption, audit logs, GDPR (others not publicly stated)
Integrations & Ecosystem
Integrates deeply with Microsoft security stack and third-party tools.
- Microsoft Sentinel
- Azure AD
- Endpoint Manager
- SIEM platforms
Support & Community
Strong enterprise support with extensive documentation and community resources.
#2 — Netskope CASB
Short description: Netskope provides a cloud-native CASB with strong data protection and real-time visibility. It focuses heavily on secure web and SaaS access with granular policy enforcement. Known for performance and scalability, it is widely adopted in enterprises. Offers both API and inline protection. Strong analytics capabilities enhance visibility.
Key Features
- Advanced DLP
- Real-time policy enforcement
- Cloud app risk assessment
- User behavior analytics
- API and inline controls
Pros
- Strong real-time protection
- High scalability
Cons
- Pricing can be premium
- Setup complexity
Platforms / Deployment
Cloud
Security & Compliance
Encryption, RBAC, audit logs, GDPR (others not publicly stated)
Integrations & Ecosystem
Supports integration with major enterprise tools.
- SIEM tools
- Identity providers
- Endpoint security tools
Support & Community
Enterprise-grade support with dedicated account management.
#3 — McAfee MVISION Cloud
Short description: A comprehensive CASB platform offering strong DLP, threat protection, and compliance features. Designed for multi-cloud environments with deep visibility into user activity. Supports a wide range of SaaS applications. Ideal for enterprises with strict compliance needs. Offers robust API-based security.
Key Features
- Data protection policies
- Threat detection
- Compliance monitoring
- Shadow IT visibility
- Encryption support
Pros
- Strong compliance features
- Multi-cloud support
Cons
- UI can feel outdated
- Complex deployment
Platforms / Deployment
Cloud
Security & Compliance
Encryption, audit logs, GDPR (others not publicly stated)
Integrations & Ecosystem
- SIEM tools
- IAM platforms
- Cloud services
Support & Community
Well-established enterprise support.
#4 — Skyhigh Security CASB
Short description: Formerly part of McAfee, Skyhigh CASB provides advanced data protection and cloud visibility. It focuses on securing SaaS applications and enforcing compliance policies. Offers both inline and API-based security. Strong analytics and reporting capabilities.
Key Features
- Data classification
- Risk assessment
- Threat protection
- Access control
- Reporting dashboards
Pros
- Strong analytics
- Flexible deployment
Cons
- Learning curve
- Pricing not transparent
Platforms / Deployment
Cloud
Security & Compliance
RBAC, audit logs, GDPR (others not publicly stated)
Integrations & Ecosystem
- Cloud apps
- SIEM tools
- Identity providers
Support & Community
Enterprise support with onboarding assistance.
#5 — Cisco Cloudlock
Short description: A cloud-native CASB solution designed for simplicity and strong API-based integration. It offers visibility into SaaS usage and enforces policies without requiring complex infrastructure. Ideal for organizations prioritizing ease of deployment.
Key Features
- API-based security
- Threat detection
- Compliance monitoring
- User activity tracking
- Risk scoring
Pros
- Easy deployment
- Strong API model
Cons
- Limited inline capabilities
- Fewer advanced features
Platforms / Deployment
Cloud
Security & Compliance
Encryption, audit logs (others not publicly stated)
Integrations & Ecosystem
- Cisco security stack
- SaaS apps
- APIs
Support & Community
Moderate documentation and support.
#6 — Bitglass CASB
Short description: Bitglass offers a cloud-first CASB platform with strong data protection and threat defense. Known for its proxy-based architecture, it provides real-time visibility and control. Suitable for organizations needing strong inline enforcement.
Key Features
- Proxy-based security
- DLP policies
- Threat detection
- Device control
- Encryption
Pros
- Strong real-time controls
- Flexible deployment
Cons
- Complex setup
- Higher cost
Platforms / Deployment
Cloud
Security & Compliance
Encryption, RBAC, audit logs (others not publicly stated)
Integrations & Ecosystem
- Cloud apps
- Security tools
- APIs
Support & Community
Enterprise-level support.
#7 — Palo Alto Networks Prisma SaaS
Short description: Prisma SaaS provides CASB capabilities within Palo Alto’s broader security platform. Focuses on SaaS security posture management and compliance. Offers deep visibility and policy enforcement across cloud applications.
Key Features
- SaaS security posture
- Threat detection
- Data protection
- Compliance monitoring
- Risk assessment
Pros
- Strong security ecosystem
- Comprehensive coverage
Cons
- Requires Palo Alto ecosystem
- Pricing complexity
Platforms / Deployment
Cloud
Security & Compliance
Encryption, audit logs, GDPR (others not publicly stated)
Integrations & Ecosystem
- Palo Alto tools
- SIEM
- Cloud platforms
Support & Community
Strong enterprise support.
#8 — Forcepoint CASB
Short description: Forcepoint CASB focuses on data-centric security and insider threat prevention. It provides visibility and control across cloud applications with strong DLP capabilities. Ideal for compliance-heavy industries.
Key Features
- Data-centric security
- Insider threat detection
- DLP
- Access control
- Analytics
Pros
- Strong DLP
- Good compliance support
Cons
- UI complexity
- Limited SMB focus
Platforms / Deployment
Cloud
Security & Compliance
DLP, encryption, audit logs (others not publicly stated)
Integrations & Ecosystem
- Security tools
- Cloud apps
- APIs
Support & Community
Enterprise-focused support.
#9 — Lookout CASB
Short description: Lookout CASB emphasizes mobile and endpoint-aware cloud security. It provides visibility into cloud usage while integrating with mobile threat defense. Suitable for mobile-first organizations.
Key Features
- Mobile security integration
- Cloud visibility
- Threat detection
- Access control
- Risk analytics
Pros
- Strong mobile focus
- Easy deployment
Cons
- Limited enterprise depth
- Smaller ecosystem
Platforms / Deployment
Cloud
Security & Compliance
Encryption, audit logs (others not publicly stated)
Integrations & Ecosystem
- Mobile security tools
- SaaS apps
- APIs
Support & Community
Moderate support availability.
#10 — Oracle CASB Cloud Service
Short description: Oracle CASB provides visibility and control over cloud applications with strong analytics and compliance capabilities. It integrates well with Oracle Cloud services. Suitable for enterprises already using Oracle ecosystem.
Key Features
- Risk analytics
- Compliance monitoring
- Threat detection
- Access control
- Data protection
Pros
- Strong analytics
- Oracle integration
Cons
- Limited flexibility
- Smaller ecosystem
Platforms / Deployment
Cloud
Security & Compliance
Encryption, audit logs (others not publicly stated)
Integrations & Ecosystem
- Oracle Cloud
- Enterprise tools
- APIs
Support & Community
Enterprise support with documentation.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Microsoft Defender | Microsoft ecosystem | Web | Cloud/Hybrid | Native integration | N/A |
| Netskope | Enterprise security | Web | Cloud | Real-time control | N/A |
| McAfee MVISION | Compliance-heavy orgs | Web | Cloud | Strong DLP | N/A |
| Skyhigh CASB | Analytics-focused teams | Web | Cloud | Reporting | N/A |
| Cisco Cloudlock | Simplicity | Web | Cloud | API-first | N/A |
| Bitglass | Inline control | Web | Cloud | Proxy-based security | N/A |
| Prisma SaaS | Palo Alto users | Web | Cloud | SaaS posture mgmt | N/A |
| Forcepoint | Data-centric security | Web | Cloud | Insider threat detection | N/A |
| Lookout | Mobile-first orgs | Web | Cloud | Mobile security | N/A |
| Oracle CASB | Oracle users | Web | Cloud | Risk analytics | N/A |
Evaluation & Scoring of Cloud Access Security Brokers (CASB)
| Tool Name | Core | Ease | Integrations | Security | Performance | Support | Value | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Microsoft Defender | 9 | 8 | 9 | 9 | 9 | 9 | 8 | 8.8 |
| Netskope | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.5 |
| McAfee MVISION | 8 | 7 | 8 | 9 | 8 | 8 | 7 | 8.0 |
| Skyhigh | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.9 |
| Cisco Cloudlock | 7 | 8 | 7 | 7 | 8 | 7 | 8 | 7.6 |
| Bitglass | 8 | 6 | 7 | 8 | 8 | 7 | 7 | 7.7 |
| Prisma SaaS | 9 | 7 | 8 | 9 | 8 | 8 | 7 | 8.2 |
| Forcepoint | 8 | 6 | 7 | 9 | 8 | 7 | 7 | 7.8 |
| Lookout | 7 | 8 | 6 | 7 | 7 | 7 | 8 | 7.3 |
| Oracle CASB | 7 | 7 | 7 | 8 | 7 | 7 | 7 | 7.2 |
How to interpret scores:
These scores are comparative and reflect relative strengths across key criteria. A higher score indicates better overall capability, but the “best” tool depends on your specific environment, integrations, and compliance needs. Enterprise tools typically score higher in security and integrations, while simpler tools perform better in ease of use.
Which Cloud Access Security Brokers (CASB) Is Right for You?
Solo / Freelancer
CASB is usually unnecessary unless handling sensitive client data in cloud apps.
SMB
Choose Cisco Cloudlock or Lookout for simplicity and lower complexity.
Mid-Market
Consider Netskope or Bitglass for balanced security and scalability.
Enterprise
Best options include Microsoft Defender, Prisma SaaS, and McAfee MVISION.
Budget vs Premium
- Budget: Cisco Cloudlock, Lookout
- Premium: Netskope, Microsoft Defender
Feature Depth vs Ease of Use
- Easy: Cloudlock
- Advanced: Netskope, Prisma
Integrations & Scalability
- Best integrations: Microsoft Defender, Prisma
- Scalable: Netskope
Security & Compliance Needs
- High compliance: McAfee, Forcepoint
- Moderate: Lookout
Frequently Asked Questions (FAQs)
1. What is CASB and why is it important?
CASB acts as a security layer between users and cloud services. It helps enforce policies, protect data, and monitor user behavior. With increasing cloud adoption, CASB ensures organizations maintain control over sensitive information. It plays a key role in Zero Trust security models. Without CASB, visibility into SaaS usage becomes limited.
2. How does CASB differ from traditional firewalls?
Traditional firewalls focus on network traffic, while CASB focuses on cloud application security. CASB provides deeper visibility into SaaS usage and user behavior. It enforces policies based on identity, device, and risk. This makes it more suitable for modern cloud environments. Firewalls alone cannot secure SaaS apps effectively.
3. What deployment models are available for CASB?
CASB solutions offer API-based, proxy-based, or hybrid deployments. API-based models provide visibility without impacting performance. Proxy models offer real-time control but may introduce latency. Hybrid models combine both approaches for flexibility. Organizations choose based on security needs and infrastructure.
4. Is CASB part of Zero Trust architecture?
Yes, CASB is a core component of Zero Trust. It enforces access controls based on identity and context. CASB ensures that users are continuously verified before accessing cloud resources. It integrates with identity providers and security tools. This aligns with Zero Trust principles of “never trust, always verify.”
5. What are common CASB use cases?
Common use cases include shadow IT discovery, data loss prevention, compliance enforcement, and threat detection. Organizations use CASB to monitor user activity and prevent unauthorized data sharing. It also helps secure third-party integrations. CASB is widely used in regulated industries.
6. How much does CASB cost?
Pricing varies depending on deployment size, features, and vendor. Most vendors offer subscription-based pricing. Enterprise solutions tend to be more expensive due to advanced features. SMB-focused tools may provide more affordable options. Exact pricing is usually not publicly stated.
7. What integrations should I look for?
Look for integrations with identity providers, SIEM tools, endpoint security, and cloud platforms. Strong integrations improve visibility and automation. APIs are important for extending functionality. Integration with existing tools reduces complexity. It also enhances security posture.
8. Can CASB prevent insider threats?
Yes, CASB can detect unusual user behavior and enforce policies. It uses analytics to identify risky actions. This helps prevent data leaks and unauthorized access. Insider threat detection is a key capability of modern CASB tools. However, it works best when combined with other security layers.
9. How long does CASB implementation take?
Implementation time varies based on deployment model and organization size. API-based deployments can be faster and simpler. Proxy-based setups may require more configuration. Large enterprises may take weeks to fully deploy. Proper planning ensures smoother rollout.
10. What are alternatives to CASB?
Alternatives include Secure Web Gateways (SWG), Zero Trust Network Access (ZTNA), and endpoint security tools. However, these do not fully replace CASB capabilities. CASB specifically focuses on cloud app security. Many organizations use CASB alongside other security tools.
Conclusion
Cloud Access Security Brokers (CASB) have become a critical pillar of modern cybersecurity, especially in cloud-first and remote work environments. As organizations adopt more SaaS applications and shift toward Zero Trust models, CASB solutions provide the visibility, control, and protection needed to manage risks effectively. From data loss prevention to identity-driven access control, CASB tools play a central role in securing sensitive information across distributed environments.
Choosing the right CASB depends heavily on your organization’s size, existing tech stack, and compliance requirements. Enterprises may benefit from platforms like Microsoft Defender or Netskope, while smaller teams may prefer simpler solutions like Cloudlock. The best approach is to shortlist 2–3 tools, run a pilot deployment, and validate integrations, performance, and security controls before making a final decision.