Introduction
Security Information & Event Management (SIEM) tools are centralized platforms that collect, analyze, and correlate security data from across an organization’s infrastructure. They aggregate logs and events from endpoints, networks, servers, and applications to detect threats, generate alerts, and support incident response.
In today’s cybersecurity landscape—where threats are sophisticated and environments are distributed—SIEM has become a core component of security operations. Modern SIEM platforms go beyond log management by incorporating AI-driven analytics, automation, and integration with EDR, NDR, and XDR systems.
Real-world use cases:
- Centralized log collection and analysis
- Detecting security incidents and anomalies
- Supporting incident investigation and response
- Compliance reporting and auditing
- Monitoring user and system behavior
What buyers should evaluate:
- Log ingestion and correlation capabilities
- Real-time threat detection
- Integration with security tools
- Scalability and performance
- Ease of deployment and management
- Reporting and compliance features
- Automation and orchestration
- Cloud vs on-prem deployment
- Data retention capabilities
- Pricing model
Best for: Enterprises, SOC teams, cybersecurity professionals, compliance-driven organizations, and complex IT environments
Not ideal for: Small environments with minimal logging requirements
Key Trends in Security Information & Event Management (SIEM)
- AI and machine learning for threat detection
- Integration with XDR and SOAR platforms
- Cloud-native SIEM solutions
- Automation of incident response workflows
- Real-time analytics and alerting
- Behavioral analytics and anomaly detection
- Increased focus on compliance reporting
- Integration with threat intelligence feeds
- Scalable data ingestion for big data environments
- Unified security operations platforms
How We Selected These Tools (Methodology)
- Market adoption and reputation
- Strength of log management capabilities
- Threat detection and analytics performance
- Integration with modern security ecosystems
- Scalability and performance
- Ease of deployment and usability
- Compliance and reporting capabilities
- Vendor maturity and innovation
- Support and community strength
- Fit across SMB and enterprise environments
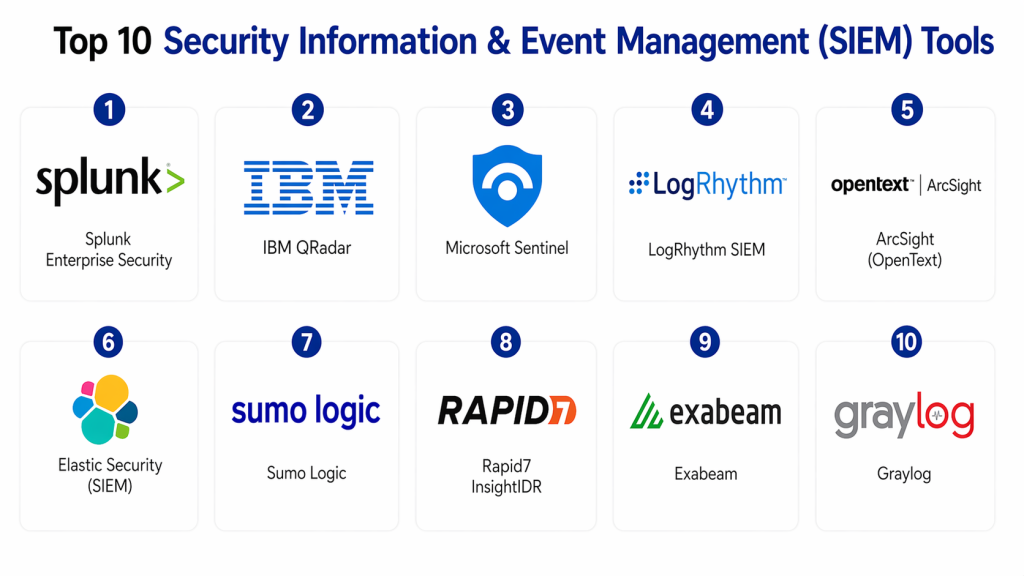
Top 10 Security Information & Event Management (SIEM) Tools
#1 — Splunk Enterprise Security
Short description :
Splunk Enterprise Security is a leading SIEM platform known for its powerful data analytics and scalability. It provides real-time monitoring and threat detection. It is widely used in enterprises. It supports advanced security operations. It offers strong customization. It is suitable for large environments.
Key Features
- Log management
- Real-time analytics
- Threat detection
- Custom dashboards
- Integration
Pros
- Highly scalable
- Powerful analytics
- Flexible
Cons
- Expensive
- Complex setup
Platforms / Deployment
- Cloud / On-prem
Security & Compliance
- RBAC, encryption
- Compliance: Not publicly stated
Integrations & Ecosystem
- APIs
- Security tools
- Data platforms
Support & Community
- Strong enterprise support
#2 — IBM QRadar
Short description :
IBM QRadar is a well-known SIEM solution providing threat detection and log management. It offers correlation and analytics. It supports compliance. It integrates with enterprise systems. It is scalable. It is widely used.
Key Features
- Log management
- Threat correlation
- Analytics
- Reporting
- Integration
Pros
- Strong analytics
- Enterprise-ready
- Reliable
Cons
- Complex
- Costly
Platforms / Deployment
- Cloud / On-prem
Security & Compliance
- RBAC, encryption
- Compliance: Not publicly stated
#3 — Microsoft Sentinel
Short description :
Microsoft Sentinel is a cloud-native SIEM platform offering advanced analytics and automation. It integrates with Microsoft ecosystem. It provides threat detection and response. It is scalable. It is easy to deploy. It is suitable for cloud environments.
Key Features
- Cloud SIEM
- Analytics
- Automation
- Threat detection
- Integration
Pros
- Cloud-native
- Scalable
- Easy deployment
Cons
- Microsoft dependency
- Configuration needed
Platforms / Deployment
- Cloud
Security & Compliance
- MFA, RBAC
- Compliance: Not publicly stated
#4 — LogRhythm SIEM
Short description :
LogRhythm provides SIEM capabilities with strong threat detection and response. It offers log management and analytics. It supports compliance. It integrates with security systems. It is scalable. It is suitable for enterprises.
Key Features
- Log management
- Threat detection
- Analytics
- Reporting
- Integration
Pros
- Strong detection
- Scalable
- Enterprise-ready
Cons
- Complex UI
- Learning curve
Platforms / Deployment
- Cloud / On-prem
Security & Compliance
- RBAC, encryption
- Compliance: Not publicly stated
#5 — ArcSight (OpenText)
Short description :
ArcSight is a SIEM solution focused on security analytics and compliance. It offers log management and correlation. It integrates with enterprise systems. It is scalable. It is suitable for large organizations. It provides strong security capabilities.
Key Features
- Log correlation
- Analytics
- Threat detection
- Compliance
- Reporting
Pros
- Strong compliance
- Scalable
- Reliable
Cons
- Complex setup
- Expensive
Platforms / Deployment
- Cloud / On-prem
Security & Compliance
- RBAC, encryption
- Compliance: Not publicly stated
#6 — Elastic Security (SIEM)
Short description :
Elastic Security provides SIEM capabilities with flexible analytics and monitoring. It integrates with Elastic stack. It supports threat detection. It is scalable. It is suitable for developers. It offers customization.
Key Features
- Log analysis
- Threat detection
- Monitoring
- Analytics
- Integration
Pros
- Flexible
- Open ecosystem
- Scalable
Cons
- Requires expertise
- Setup complexity
Platforms / Deployment
- Cloud / Self-hosted
Security & Compliance
- RBAC
- Compliance: Not publicly stated
#7 — Sumo Logic
Short description :
Sumo Logic is a cloud-native SIEM platform offering log management and analytics. It supports real-time monitoring. It integrates with SaaS tools. It is scalable. It is easy to use. It is suitable for cloud environments.
Key Features
- Log management
- Analytics
- Monitoring
- Integration
- Reporting
Pros
- Easy to use
- Cloud-native
- Scalable
Cons
- Limited customization
- Pricing concerns
Platforms / Deployment
- Cloud
Security & Compliance
- RBAC, encryption
- Compliance: Not publicly stated
#8 — Rapid7 InsightIDR
Short description :
Rapid7 InsightIDR combines SIEM with detection and response capabilities. It offers log management and analytics. It supports threat detection. It integrates with Rapid7 tools. It is scalable. It provides strong visibility.
Key Features
- Log management
- Threat detection
- Analytics
- Monitoring
- Integration
Pros
- Strong visibility
- Scalable
- Easy deployment
Cons
- Limited customization
- Cost
Platforms / Deployment
- Cloud
Security & Compliance
- MFA, RBAC
- Compliance: Not publicly stated
#9 — Exabeam
Short description :
Exabeam provides SIEM with strong analytics and user behavior monitoring. It supports threat detection and investigation. It integrates with security tools. It is scalable. It is suitable for enterprises. It offers strong automation.
Key Features
- Analytics
- User behavior monitoring
- Threat detection
- Automation
- Reporting
Pros
- Strong analytics
- Scalable
- Automation
Cons
- Complex
- Expensive
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- RBAC
- Compliance: Not publicly stated
#10 — Graylog
Short description :
Graylog is an open-source SIEM platform offering log management and analysis. It provides monitoring and analytics. It is flexible. It supports customization. It is scalable. It is suitable for developers and SMBs.
Key Features
- Log management
- Analytics
- Monitoring
- Integration
- Open platform
Pros
- Open-source
- Flexible
- Affordable
Cons
- Requires expertise
- Limited enterprise features
Platforms / Deployment
- Cloud / Self-hosted
Security & Compliance
- RBAC
- Compliance: Not publicly stated
Comparison Table
| Tool | Best For | Platform | Deployment | Feature | Rating |
|---|---|---|---|---|---|
| Splunk | Enterprise | Multi | Hybrid | Analytics | N/A |
| IBM | Enterprise | Multi | Hybrid | Correlation | N/A |
| Microsoft | Enterprise | Cloud | Cloud | Integration | N/A |
| LogRhythm | Enterprise | Multi | Hybrid | Detection | N/A |
| ArcSight | Enterprise | Multi | Hybrid | Compliance | N/A |
| Elastic | Devs | Multi | Hybrid | Open | N/A |
| Sumo Logic | Cloud | Cloud | Cloud | Simplicity | N/A |
| Rapid7 | SMB | Cloud | Cloud | Visibility | N/A |
| Exabeam | Enterprise | Multi | Hybrid | Analytics | N/A |
| Graylog | SMB | Multi | Hybrid | Open-source | N/A |
Evaluation & Scoring of SIEM Tools
| Tool | Core | Ease | Integration | Security | Performance | Support | Value | Total |
|---|---|---|---|---|---|---|---|---|
| Splunk | 10 | 7 | 9 | 10 | 9 | 9 | 7 | 8.9 |
| IBM | 9 | 7 | 8 | 9 | 8 | 8 | 7 | 8.2 |
| Microsoft | 9 | 9 | 10 | 9 | 9 | 9 | 9 | 9.2 |
| LogRhythm | 9 | 7 | 8 | 9 | 8 | 8 | 7 | 8.2 |
| ArcSight | 9 | 6 | 8 | 9 | 8 | 8 | 7 | 8.1 |
| Elastic | 8 | 7 | 9 | 8 | 8 | 7 | 9 | 8.2 |
| Sumo Logic | 8 | 9 | 8 | 8 | 8 | 8 | 8 | 8.3 |
| Rapid7 | 8 | 9 | 8 | 8 | 8 | 8 | 8 | 8.3 |
| Exabeam | 9 | 7 | 8 | 9 | 8 | 8 | 7 | 8.2 |
| Graylog | 8 | 7 | 7 | 8 | 8 | 7 | 9 | 8.0 |
Which SIEM Tool Is Right for You?
Solo / Freelancer
- Graylog
SMB
- Rapid7, Sumo Logic
Mid-Market
- Elastic, LogRhythm
Enterprise
- Splunk, Microsoft, IBM
Budget vs Premium
- Budget → Graylog
- Premium → Splunk
Feature Depth vs Ease
- Easy → Sumo Logic
- Advanced → Splunk
Integrations & Scalability
- Best → Microsoft Sentinel
Security Needs
- High security → Splunk
Frequently Asked Questions (FAQs)
1. What is Security Information & Event Management (SIEM)?
SIEM is a security solution that collects and analyzes logs and events from across an organization’s IT environment. It helps detect suspicious activity and potential threats in real time. SIEM platforms provide centralized visibility into security events. They are essential for monitoring and managing security operations.
2. Why is SIEM important for organizations?
SIEM is important because it helps organizations detect and respond to security threats quickly. It centralizes data from multiple systems, making it easier to identify anomalies. It also supports compliance by maintaining logs and audit trails. This improves overall security visibility and control.
3. How does SIEM work?
SIEM works by collecting logs from various sources such as servers, endpoints, and network devices. It then analyzes and correlates this data to detect patterns or anomalies. When a potential threat is identified, alerts are generated. This allows security teams to investigate and respond promptly.
4. Who should use SIEM solutions?
SIEM solutions are primarily used by enterprises, IT teams, and Security Operations Centers (SOCs). They are ideal for organizations with complex IT environments and high security requirements. Companies that must meet compliance standards also benefit from SIEM. It is especially useful in large-scale environments.
5. Is SIEM scalable for large environments?
Yes, modern SIEM platforms are highly scalable and can handle large volumes of data. Cloud-based SIEM solutions allow organizations to scale as their data grows. This makes them suitable for enterprises with distributed systems. Scalability ensures consistent monitoring and performance.
6. What is the difference between SIEM and SOAR?
SIEM focuses on collecting and analyzing security data to detect threats. SOAR focuses on automating the response to those threats. While SIEM generates alerts, SOAR helps take action based on those alerts. Both tools work together to improve security operations efficiency.
7. Does SIEM support real-time threat detection?
Yes, most modern SIEM tools support real-time monitoring and threat detection. They analyze incoming data continuously to identify suspicious activities. This allows organizations to respond to threats quickly. Real-time capabilities are critical for minimizing damage
8. Is SIEM enough for complete security?
SIEM is a key component of cybersecurity, but it is not sufficient on its own. Organizations should combine it with tools like EDR, XDR, and network security solutions. A layered security approach provides better protection. SIEM acts as the central visibility layer.
9. Is SIEM difficult to implement?
SIEM implementation can be complex, especially in large environments. It requires proper configuration and integration with existing systems. However, many modern cloud-based SIEM tools simplify deployment. With proper planning, implementation becomes manageable.
10. What are alternatives to SIEM?
SIEM works alongside solutions like XDR, EDR, and log management tools. These tools focus on different aspects of security. They are not replacements but complementary technologies. Together, they create a more comprehensive security strategy.
Conclusion
Security Information & Event Management (SIEM) tools are essential for modern cybersecurity operations, providing centralized visibility, threat detection, and incident response capabilities. As cyber threats become more complex, SIEM platforms have evolved to include AI-driven analytics, automation, and integration with broader security ecosystems.
The right SIEM solution depends on your organization’s size and needs. Enterprise platforms like Splunk and Microsoft Sentinel offer advanced capabilities, while solutions like Graylog and Sumo Logic provide flexibility and affordability. Organizations should evaluate their requirements, test solutions, and implement SIEM as part of a comprehensive security strategy