Introduction
Penetration Testing Tools are cybersecurity solutions used to simulate real-world attacks on systems, networks, and applications to identify security weaknesses. Unlike vulnerability scanners, these tools actively test defenses by mimicking hacker techniques to uncover exploitable flaws.
In today’s cybersecurity landscape, where threats are becoming more advanced, penetration testing is essential for validating security controls. Modern tools support automation, AI-assisted testing, and integration with DevSecOps pipelines, enabling continuous security validation.
Real-world use cases:
- Simulating cyberattacks to identify vulnerabilities
- Testing web applications and APIs for security flaws
- Assessing network security posture
- Validating compliance and security controls
- Supporting red team and ethical hacking exercises
What buyers should evaluate:
- Coverage (network, web, API, cloud)
- Automation vs manual testing capabilities
- Ease of use and learning curve
- Integration with security tools
- Reporting and documentation
- Scalability across environments
- Community and support
- Platform compatibility
- Open-source vs commercial options
- Pricing and licensing
Best for: Security professionals, ethical hackers, penetration testers, SOC teams, and enterprises
Not ideal for: Non-technical users or organizations without security expertise
Key Trends in Penetration Testing Tools
- Increased use of AI-assisted penetration testing
- Integration with DevSecOps pipelines
- Automated penetration testing platforms
- Expansion into cloud and API security testing
- Continuous security validation
- Growth of open-source security tools
- Focus on real-time attack simulation
- Integration with vulnerability management platforms
- Increased use in red team exercises
- Hybrid manual + automated testing approaches
How We Selected These Tools (Methodology)
- Industry adoption and reputation
- Coverage across testing areas
- Depth of testing capabilities
- Integration with security ecosystems
- Ease of use and flexibility
- Community support and documentation
- Scalability and performance
- Open-source and enterprise balance
- Vendor maturity and innovation
- Fit across different skill levels
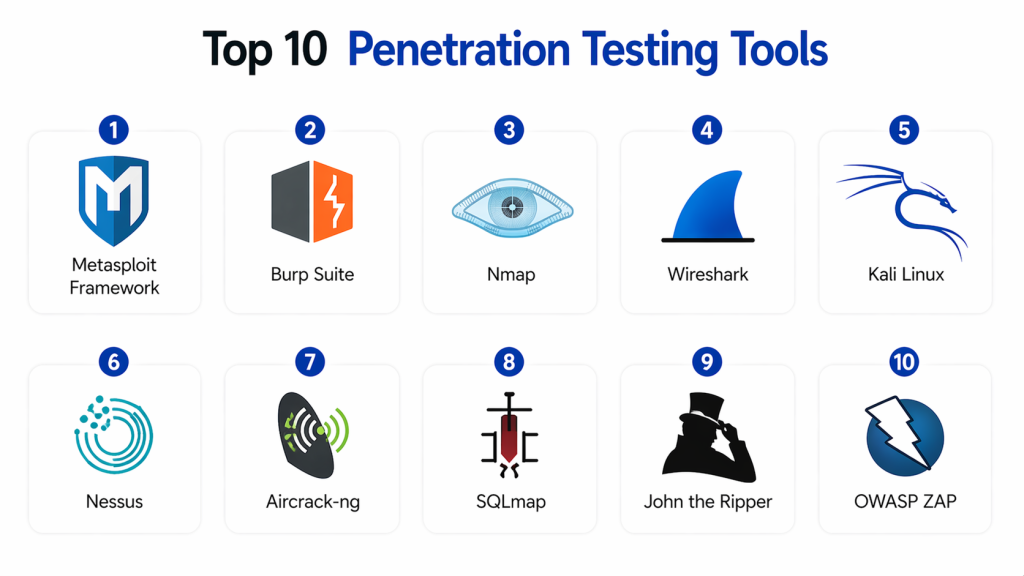
Top 10 Penetration Testing Tools
#1 — Metasploit Framework
Short description:
Metasploit is one of the most widely used penetration testing tools for exploit development and testing. It provides a large database of exploits. It is highly flexible. It is used by security professionals. It supports automation. It is suitable for advanced testing.
Key Features
- Exploit database
- Payload generation
- Automation
- Integration
- Testing frameworks
Pros
- Highly flexible
- Strong community
- Powerful
Cons
- Requires expertise
- Complex for beginners
Platforms / Deployment
- Windows / Linux / macOS
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- APIs
- Security tools
Support & Community
- Large open-source community
#2 — Burp Suite
Short description :
Burp Suite is a popular tool for web application penetration testing. It offers both manual and automated testing features. It is widely used by security professionals. It supports scanning and analysis. It is flexible. It is suitable for developers and testers.
Key Features
- Web scanning
- Manual testing
- Proxy tools
- Automation
- Reporting
Pros
- Powerful features
- Widely used
- Flexible
Cons
- Requires expertise
- Paid version needed for full features
Platforms / Deployment
- Windows / macOS / Linux
Security & Compliance
- Not publicly stated
#3 — Nmap
Short description:
Nmap is a widely used network scanning tool for discovering hosts and services. It is essential for reconnaissance in penetration testing. It provides detailed network information. It is lightweight. It is open-source. It is widely used.
Key Features
- Network scanning
- Port scanning
- Service detection
- OS detection
- Scripting engine
Pros
- Fast
- Lightweight
- Open-source
Cons
- Limited exploitation features
- Requires expertise
Platforms / Deployment
- Windows / Linux / macOS
Security & Compliance
- Not publicly stated
#4 — Wireshark
Short description :
Wireshark is a network protocol analyzer used for capturing and analyzing network traffic. It helps identify vulnerabilities in communication. It is widely used. It provides deep insights. It is flexible. It supports detailed analysis.
Key Features
- Packet analysis
- Traffic monitoring
- Protocol inspection
- Filtering
- Reporting
Pros
- Deep analysis
- Free
- Widely used
Cons
- Complex
- Not a full pentest tool
Platforms / Deployment
- Windows / Linux / macOS
Security & Compliance
- Not publicly stated
#5 — Kali Linux
Short description :
Kali Linux is a penetration testing distribution that includes numerous security tools. It is widely used by ethical hackers. It provides a complete testing environment. It is flexible. It is open-source. It is suitable for professionals.
Key Features
- Pre-installed tools
- Security testing environment
- Network testing
- Web testing
- Exploitation
Pros
- Comprehensive
- Flexible
- Free
Cons
- Requires expertise
- Not beginner-friendly
Platforms / Deployment
- Linux
Security & Compliance
- Not publicly stated
#6 — Nessus
Short description :
Nessus is a vulnerability scanning tool also used in penetration testing workflows. It detects vulnerabilities and misconfigurations. It provides reports. It is easy to use. It is scalable. It is widely adopted.
Key Features
- Vulnerability scanning
- Reporting
- Risk scoring
- Compliance
- Integration
Pros
- Easy to use
- Accurate
- Scalable
Cons
- Limited exploitation
- Paid license
Platforms / Deployment
- Windows / Linux
Security & Compliance
- RBAC
- Compliance: Not publicly stated
#7 — Aircrack-ng
Short description :
Aircrack-ng is a tool for testing wireless network security. It is used for cracking Wi-Fi passwords. It supports network auditing. It is widely used. It is flexible. It is suitable for wireless testing.
Key Features
- Wi-Fi testing
- Packet capture
- Password cracking
- Monitoring
- Analysis
Pros
- Strong wireless testing
- Free
- Flexible
Cons
- Limited scope
- Requires expertise
Platforms / Deployment
- Linux / Windows
Security & Compliance
- Not publicly stated
#8 — SQLmap
Short description :
SQLmap is an open-source tool for testing SQL injection vulnerabilities. It automates database exploitation. It is widely used. It is flexible. It is scalable. It is suitable for web testing.
Key Features
- SQL injection testing
- Automation
- Database access
- Reporting
- Integration
Pros
- Powerful
- Automated
- Free
Cons
- Limited scope
- Requires knowledge
Platforms / Deployment
- Windows / Linux
Security & Compliance
- Not publicly stated
#9 — John the Ripper
Short description :
John the Ripper is a password cracking tool used in penetration testing. It helps test password strength. It supports multiple formats. It is flexible. It is widely used. It is suitable for security testing.
Key Features
- Password cracking
- Hash analysis
- Automation
- Reporting
- Integration
Pros
- Powerful
- Flexible
- Free
Cons
- Requires expertise
- Limited UI
Platforms / Deployment
- Windows / Linux / macOS
Security & Compliance
- Not publicly stated
#10 — OWASP ZAP
Short description :
OWASP ZAP is an open-source web application security scanner. It helps detect vulnerabilities in web apps. It is easy to use. It supports automation. It is widely used. It is suitable for beginners and professionals.
Key Features
- Web scanning
- Automation
- Vulnerability detection
- Reporting
- Integration
Pros
- Free
- Easy to use
- Flexible
Cons
- Limited advanced features
- Slower than premium tools
Platforms / Deployment
- Windows / Linux / macOS
Security & Compliance
- Not publicly stated
Comparison Table
| Tool | Best For | Platform | Deployment | Feature | Rating |
|---|---|---|---|---|---|
| Metasploit | Advanced | Multi | Local | Exploits | N/A |
| Burp | Web | Multi | Local | Web testing | N/A |
| Nmap | Network | Multi | Local | Scanning | N/A |
| Wireshark | Network | Multi | Local | Analysis | N/A |
| Kali | All | Linux | Local | Toolkit | N/A |
| Nessus | SMB | Multi | Hybrid | Scanning | N/A |
| Aircrack | Wireless | Multi | Local | Wi-Fi | N/A |
| SQLmap | Web | Multi | Local | SQL testing | N/A |
| John | Passwords | Multi | Local | Cracking | N/A |
| OWASP ZAP | Web | Multi | Local | Scanning | N/A |
Evaluation & Scoring of Penetration Testing Tools
| Tool | Core | Ease | Integration | Security | Performance | Support | Value | Total |
|---|---|---|---|---|---|---|---|---|
| Metasploit | 10 | 7 | 9 | 10 | 9 | 9 | 8 | 9.0 |
| Burp | 9 | 8 | 8 | 9 | 8 | 8 | 8 | 8.5 |
| Nmap | 8 | 7 | 7 | 8 | 9 | 8 | 9 | 8.2 |
| Wireshark | 8 | 6 | 7 | 8 | 9 | 8 | 9 | 8.1 |
| Kali | 9 | 7 | 8 | 9 | 8 | 8 | 9 | 8.5 |
| Nessus | 9 | 9 | 8 | 9 | 9 | 8 | 8 | 8.8 |
| Aircrack | 7 | 6 | 6 | 7 | 8 | 7 | 9 | 7.5 |
| SQLmap | 8 | 7 | 7 | 8 | 8 | 7 | 9 | 8.0 |
| John | 8 | 6 | 6 | 8 | 8 | 7 | 9 | 7.9 |
| OWASP ZAP | 8 | 8 | 7 | 8 | 8 | 8 | 9 | 8.2 |
Which Penetration Testing Tool Is Right for You?
Solo / Freelancer
- OWASP ZAP, Nmap
SMB
- Nessus, Burp Suite
Mid-Market
- Metasploit, Kali Linux
Enterprise
- Metasploit, Burp Suite
Budget vs Premium
- Budget → OWASP ZAP
- Premium → Burp Suite
Feature Depth vs Ease
- Easy → OWASP ZAP
- Advanced → Metasploit
Integrations & Scalability
- Best → Metasploit
Security Needs
- High security → Metasploit
Frequently Asked Questions (FAQs)
1. What are Penetration Testing Tools?
Penetration testing tools are used to simulate cyberattacks on systems and applications. They help identify vulnerabilities that attackers could exploit. These tools are commonly used by ethical hackers and security teams. They provide insights into system weaknesses and help improve overall security.
2. Why are penetration testing tools important?
These tools are important because they help organizations proactively identify and fix security gaps. By simulating real-world attacks, they reveal vulnerabilities that scanners may miss. This reduces the risk of data breaches. They are essential for maintaining strong cybersecurity defenses.
3. How do penetration testing tools work?
They work by scanning systems, analyzing vulnerabilities, and attempting to exploit weaknesses. Some tools automate testing, while others support manual analysis. They generate reports detailing vulnerabilities and risks. This helps teams take corrective actions.
4. Who should use penetration testing tools?
These tools are mainly used by security professionals, ethical hackers, and IT teams. Organizations with sensitive data benefit the most from them. They are also used in compliance and security audits. Skilled users can maximize their effectiveness.
5. Are penetration testing tools scalable?
Yes, many modern tools are scalable and can be used across large environments. They support testing of networks, applications, and cloud systems. Cloud-based tools make scaling easier. This ensures consistent testing coverage.
6. Do penetration testing tools integrate with other tools?
Yes, they integrate with vulnerability scanners, SIEM, and DevSecOps tools. This helps create a complete security ecosystem. Integration improves workflow automation. It allows better coordination between security processes.
7. Are penetration testing tools secure?
Yes, these tools are safe when used by authorized professionals. They are designed for ethical use in controlled environments. Proper configuration is important to avoid unintended impact. They help strengthen security rather than weaken it.
8. Are penetration testing tools difficult to use?
Some tools are easy to use, while others require advanced technical knowledge. Open-source tools often have a learning curve. Training and experience improve usability. Choosing the right tool depends on skill level.
9. What are alternatives to penetration testing tools?
Alternatives include vulnerability scanning and security audits. However, these methods may not simulate real attacks. Penetration testing provides deeper insights. It is often used alongside other security practices.
10. Are penetration testing tools expensive?
Pricing varies depending on the tool and features. Many open-source tools are free. Enterprise tools can be costly. Investing in these tools helps prevent expensive security breaches.
Conclusion
Penetration Testing Tools are essential for identifying and validating security weaknesses by simulating real-world attacks. As cyber threats continue to evolve, these tools help organizations proactively strengthen their defenses and reduce risk exposure.
The right tool depends on your skill level and requirements. Tools like Metasploit and Burp Suite provide advanced capabilities, while options like OWASP ZAP and Nmap offer cost-effective solutions. Organizations should evaluate their needs, test tools, and integrate penetration testing into their overall security strategy.